It wouldn’t be work if we didn’t have more than one different, yet similar, things going on in the office at any given time. The disaster recovery user testing is drawing to a close and I’ll be the first to admit that opening it up to users has certainly been a learning experience. (More on that later.)
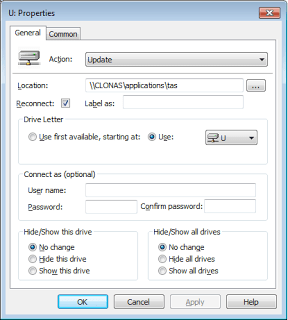
Meanwhile, in an attempt to phase out our Citrix Remote Access farm, we’ve started to “soft-launch” our production version of Windows 2008 Terminal Services using Terminal Services Web Access and RemoteApp. Two applications we are publishing as remote applications are our financial system and our timecard system. We succeeding in getting both these applications mostly running in our disaster recovery lab last month, but our production version of Terminal Services is a different animal.
In the disaster lab, I didn’t configure any special group policies that affected Internet Explorer or any other functions. The setup was just by the basic configuration wizards for Terminal Services, TS Gateway and RemoteApp. Our production version of Terminal Services was set up “by the book” (particularly this book) with lots of security customizations added on with group policies. I’m all for tightening things down until people squeal and then loosening things up as needed and my co-worker had done just that with this installation.
Today, I tested out the timecard application that requires a Java plug-in. The plug-in automatically initializes on our regular desktop machines without issue. On the Terminal Server, which is running the Enhanced Security Configuration, the name of server hosting time timecard web page must be part of the “Intranet” security zone in IE.
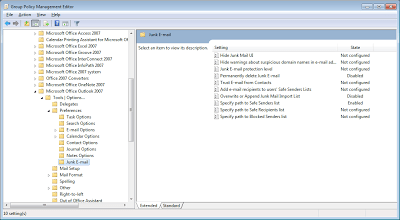
Easy fix… except I don’t have access to the “Tools – Internet Options” pages in Internet Explorer with my regular user account. That’s a group policy setting. Or rather, 3 group policy settings. Because the options available in group policy have grown as each new OS has been introduced, there are several places you can enable, disable and tweak various aspects of what IE menus are available to users. It took me several visits to our Terminal Services policies to restore access to the “security” tab of Internet Options.
Sure enough, once I added the proper web server to the Intranet list, the plug-in initialized. But we don’t want to have to explain this to each and every user when they access remote applications for the first time. So next up was getting those setting to automatically configured for each new user.
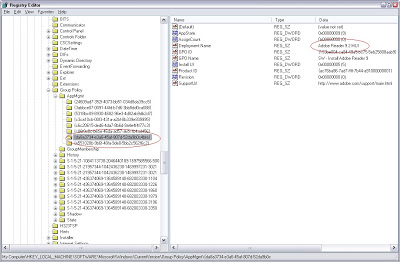
Our first stop was Group Policy Preferences, which allows for configuration of much of the Internet Options tabs, but not any of the lists for Intranet, Trusted or Restricted sites – how frustrating. But those are simply registry keys, which can be added “a la carte” with Group Policy Preferences as well. The end seems near.
A quick search yields this MSDN article, Adding Sites to the Enhanced Security Configuration Zones. We ended up adding registry keys for both the regular non-ESC domains and the ESC domains because our testing showed that my user account put zone additions in the regular domain area and my co-worker’s went in the EscDomain registry area. (The dword hex of 1 means “Intranet zone”, use 2 for “Trusted” sites.)
- [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\timecard]
“http”=dword:00000001
- [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\EscDomains\timecard]
“http”=dword:00000001
We didn’t experiment further with the “Domain” vs “EscDomain” mystery, instead just added registry keys to cover all our bases for the time being. Now the only thing left is to decide if we want to take away those IE Options pages that I added back in for testing. Jury is still out on that one.