As IT Professionals, we often have a lot of projects on our plates, as do the people we support in our businesses. These days, remote access to work resources isn’t a bonus, it’s a requirement. How do you make sure employees have access to the work resources they need while keeping them secure?
One common solution that’s been used for a while now is Remote Desktop Services. Formerly known as Terminal Services, RDS provides a rich desktop or application experience and has evolved a lot since its debut in NT 4.0. One of the most useful features of RDS in recent years has been RemoteApp. RemoteApp enables you to make programs that are accessed remotely through Remote Desktop Services appear as if they are running on the end user’s local computer. Instead of being presented to the user in the desktop of the Remote Desktop Session Host (RD Session Host) server, the RemoteApp program is integrated with the client’s desktop.
When it comes to implementing Remote Desktop Services within Azure, you have two choices:
- Implement a full infrastructure like you would do on-prem, with a Session Host, Web Access and Broker server roles. This gives you full control from the OS up and is a potential option if you are looking to lift-and-shift your existing RDS infrastructure into the cloud.
- Customize an image to use with Azure RemoteApp.
For that first option, simply lifting and shifting the RDS servers to Azure can give you some quick benefits. In many cases your RDS users are coming from outside your corporate network, thus moving those servers to Azure would relieve your on-prem network connect of that traffic load. Plus Azure gives you the ability to scale up or scale out with ease – allowing you to adjust to any change in workload without incurring additional CAPEX costs for hardware.
For a great step-by-step guidance on building you own RDS infrastructure in Azure, I encourage you to read Keith Mayer’s comprehensive posts
Part I and
Part 2 of RDS on Azure.
Now for that second option, customize an image to use with Azure RemoteApp, I suggest considering using a customized image because chances are you use more applications than just the Microsoft Office Suite. (If you happen to use just Office 365, there is an image for that already!) You also have two choices to make within Azure RemoteApp – cloud only or hybrid. With a cloud collection the data and applications are held in Azure, with no connection to your on-prem network. With a hybrid collection the data and applications are still hosted in Azure, but also lets users access data and resources stored on your local network.
With either customized option, you are responsible for the management and maintenance of that image, however that is still less maintenance than managing and maintaining all the servers required for a traditional RDS infrastructure. Plus, Azure Remote app handles all the scaling needs based on the number of subscribers you authorize.
Combine that with the fact that Azure RemoteApp is supported on Windows, Windows RT, as well as on the Remote Desktop apps for Mac, iOS, and Android, and you’ve got a robust way to let users access resources from any device.
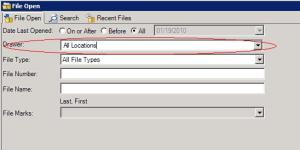
To get started with RemoteApp on Azure, you will need an image
which isn’t trivial. If you want to do the hybrid collection you will also need to consider how to sync your on-prem directory to Azure AD, this
roadmap can help. There is also an easy to implement trial that just includes 30 days of Office 2013 Professional Plus, but that trial can’t be converted to a production RemoteApp installation after the trial ends.
So what is right for your organization? Only you can say. But I have my short list of things I’d move to Azure and RDS would be right up there with SharePoint deployments. Hybrid collections provide the most complete experience since user will be able to access on-premises resources like they can with RDS you provide on-prem now. But cloud collections provide an easy way to isolate your deployment, which could meet at audit requirement or limit access for a specific set of workers.
If you already have a VNET in place with Azure, lifting and shifting RDS might be what you are most comfortable with. At this writing, RemoteApp can’t use an existing VNET, but you can connect the RemoteApp VNET to an existing one if need be. For more information about Azure RemoteApp, I highly recommend starting with the online documentation.